Why does your business need identity management?
Every organization needs to protect itself and its information. Depending on the industry you’re in or the type of business you operate, you may need different protections and solutions than your neighbor. Identity and access management and privileged access management is vital to the security of your organization. The business drivers behind identity governance include efficiencies, client experience, role based approach, segregation of duties, compliance, security, reports/dashboards, and access certification.

IGA
is a critical component of IDM, focused on managing and enforcing policies and controls around human and non-human access to resources and data. It involves defining roles and responsibilities, establishing policies and procedures, and enforcing them through onboarding and off-boarding, request and approval processes, access certification, audits, and compliance reporting.

IAM
is the process of managing the identities of individuals within an organization and controlling access to resources and data. These processes can be implemented through a variety of technologies, including directory services, single sign-on (SSO), and multi-factor authentication (MFA).

PAM
is focused on securing and managing access to privileged accounts, such as those used by system administrators and IT staff. It involves monitoring and controlling access to these accounts, granting privileges just-in-time, enforcing strong authentication and authorization policies, and auditing activity to ensure compliance with security policies and regulations. Some solutions are beginning to use ephemeral accounts to completely eliminate attack surface.

DAG
is focused on governing access to sensitive data and ensuring that data is used appropriately. It involves locating and classifying sensitive data, defining data access policies and controls, monitoring and auditing data access, and enforcing compliance with regulations and policies related to data privacy and security.
In summary, IDM, including its components IGA, IAM, PAM, and DAG, is critical for ensuring the security and privacy of sensitive data within an organization. By managing identities, access rights, and data access, organizations can control who has access to what information, and monitor and audit activity to ensure compliance with security policies and regulations.
There are many business drivers that steer organizations to thoroughly understand how IGA can enhance their overall IDM program.
Expand Content
- Streamline user provisioning and deprovisioning processes
- Empower users with self-service capabilities
- Reduce help desk inquiries and improve response times
- Establish a common security infrastructure for consistent access management
- Automate onboarding and offboarding workflows for workforce management
- Meet regulatory requirements such as HIPAA, SOX, GDPR, and PCI
- Track and audit user access for compliance reporting
- Easily identify who has access to applications and data
- Provide reporting to auditors and regulators for transparency and accountability
- Improve the overall user experience with seamless access to applications and resources
- Simplify application development and deployment
- Accelerate user productivity with immediate access to key applications
- Automate user administration tasks to reduce errors and delays
- Use Intelligence to make recommendations for approval and certification tasks
- Increase accuracy and precision of identity privileges
- Expedite off-boarding processes for departing users
- Reduce risk of dormant, orphaned, or over-privileged accounts
- Strengthen access controls and reduce the risk of unauthorized access
- Enforce least-privilege access to reduce the risk of unintentional or malicious data breaches
Expand Content
- Establish clear visibility into business functions and match them with access definitions
- Manage access through roles for consistency and simplicity
- Create clarity around access to meet business needs
- Automatically drive access provisioning and deprovisioning through Identity lifecycle events
- Use Artificial Intelligence to take your RBAC program to the next level
- Provide a comprehensive view of access-related data and violations
- Automatically collect, correlate, and audit identity data from multiple enterprise resources
- Gain transparency into access management and support business decisions with actionable insights
- Define audit policies at role or entitlement levels within an application or across applications
- Automatically identify imminent violations when users are provisioned, including when job transfers occur
- Proactively notify requesters that new access requests will result in a risky policy violation
- Maintain an ongoing record of activities with an impact on SoD compliance
- Certify user access in a timely and efficient manner
- Conduct certification at role, application, entitlement, and user levels
- Revoke noncompliant user accounts to minimize risk
- Automate provisioning workflows to reduce compliance gaps and increase coverage.
- Use Artificial Intelligence to make informed decisions
Zirous has the identity management solutions you need.
Identity Management (IDM) projects can be complex and challenging, with business requirements and processes that can be even more difficult than the technical implementation itself.
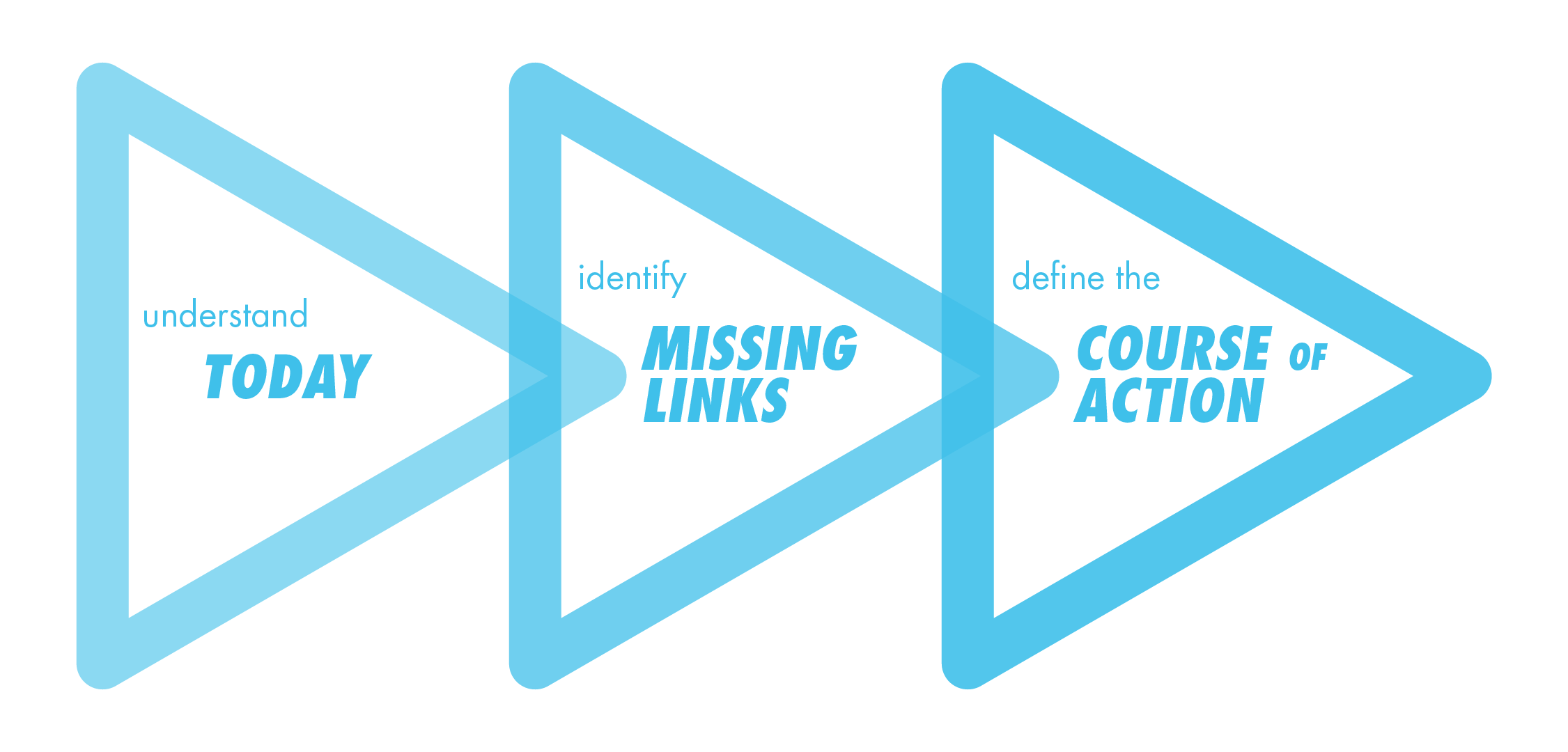
As a strategic partner, we understand that timely and accurate security access is critical to the success of your organization, and we are committed to helping you achieve your goals. We begin by taking a top-down approach, thoroughly understanding your business and goals, as well as the current state of your IDM program. We assess your capabilities, users, desired flexibility, and more, and then make recommendations for both a product and business processes that meet your needs. We also develop a framework plan and break down the project into manageable phases.
We remain closely involved in the project through the implementation, working side-by-side with your team to configure the system, anticipating and addressing any bumps in the road that may arise. We celebrate milestones with you, and our experts are always available to help ensure a successful IDM implementation.
Our experience and expertise make us the ideal partner for organizations seeking to improve their identity and access management processes. While every journey is unique, we are committed to being there every step of the way to help you achieve your goals.
Catalyst
Get started with a Catalyst!
Catalyst, our comprehensive Discovery process, delivers an Identity Management (IDM) strategy and roadmap that paves the way to an automated and secure future for your organization.
Catalyst is designed for organizations that:
- Recognize the critical importance of securing human and non-human access
- Seek to optimize user lifecycle management by automating processes related to onboarding, off-boarding, job transfers, and more
- Are committed to streamlining and automating audit and compliance processes
- Understand the value of centralizing human and non-human access information from multiple systems for greater efficiency and visibility.
Through Catalyst, we work closely with your organization to identify areas for improvement, assess your current capabilities and needs, and develop a comprehensive IDM roadmap that addresses your unique challenges and goals. Zirous analysts will challenge your organization to realign and re-invigorate your business processes to take advantage of our experience and best practices. Our experienced team is committed to guiding you every step of the way towards a more secure and efficient IAM program that meets your specific needs.

Verticals
z|Detect Assessments

Identity Assessment Scorecard
Analyze your current practices and identify areas to better align with industry best practices.

OIM Health Check
Take a deep dive into your OIM system to ensure it’s performing at its very best.













