You still have
until your security breach is resolved.
Or… you could create a preventative solution.
It’s not if. It’s when.
Whether you’re small and local or huge and global, you’re at risk for a security breach. No target is too big or too small.
In fact, most breaches aren’t from external hackers looking for a huge score. 75% of security breaches stem from internal user accounts, not external hackers.

The average security breach goes undetected for 197 days, and once found, takes 69 days to contain. It costs $3.86 million to repair the average breach, and the cost of lost business is an additional $4.2 million.
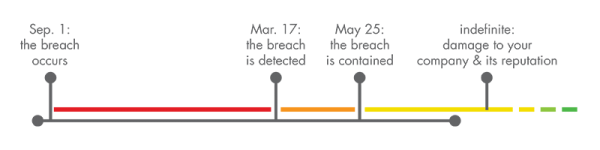
Don’t let this happen to you.
With over 75 years of experience across our identity and access management team, we have a successful, proven record of partnering with and preparing organizations to tackle their identity needs.